The landscape of global defense communication has shifted dramatically as the North Atlantic Treaty Organization officially sanctions the use of standard consumer hardware for its most sensitive operations. This certification allows military personnel to utilize iPhones and iPads for handling restricted data, effectively dismantling the long-standing requirement for specialized, ruggedized equipment that often lagged behind the private sector in terms of both speed and usability. By integrating these ubiquitous tools into its strategic framework, the alliance is acknowledging that the security architecture found in modern consumer electronics has reached a level of sophistication previously reserved for top-tier government laboratories. This transition is not merely about convenience; it represents a fundamental change in how international security organizations approach risk management and digital infrastructure in an increasingly connected world.
Establishing a New Standard for Defense Technology
Transitioning From Custom Hardware to Consumer Ecosystems
The adoption of standard iOS devices signifies a departure from the traditional “bespoke” model of military procurement, where hardware was custom-built at an enormous cost to meet specific security criteria. These legacy systems were frequently cumbersome and lacked the intuitive interfaces that modern users have come to expect, often leading to operational friction during critical missions. Apple has countered this by embedding enterprise-grade security features directly into the core of its operating systems, ensuring that every device leaving the factory possesses the same high-level protection. This strategy allows NATO to bypass the slow development cycles of specialized defense contractors and instead lean on the rapid innovation of the commercial tech sector. Consequently, the alliance can deploy the latest mobile advancements across its 32 member states with the assurance that the underlying hardware is already hardened against sophisticated cyber threats.
The integration of these devices into the NATO framework highlights a modern philosophy where security is treated as an essential component of the design phase rather than a secondary add-on. For decades, military organizations had to compromise on performance to ensure data integrity, but the current generation of mobile hardware proves that high-speed processing and robust encryption can coexist seamlessly. By making these protections accessible to the general public, the technology has undergone rigorous “stress testing” by millions of users worldwide, providing a level of reliability that custom-built hardware rarely achieves. This shift allows defense planners to focus their resources on strategic application development rather than maintaining outdated physical infrastructure. The move to a consumer-led ecosystem ensures that military personnel remain equipped with the most capable tools available, fostering a more agile and responsive defense posture across all branches of the alliance.
The Influence of International Security Audits
Before the alliance reached a consensus on this transition, the German Federal Office for Information Security conducted an exhaustive multi-year evaluation of the software and hardware architecture. This rigorous auditing process was essential to verify that the native security measures within iOS could withstand the persistent threats directed at national governments. The BSI’s findings served as the technical foundation for NATO’s certification, providing the necessary evidence that commercial platforms are capable of protecting classified information without third-party modifications. This collaboration between a leading national security agency and a private technology giant demonstrates a new era of transparency where government experts can deep-dive into proprietary code to ensure it meets international standards. Such high-level validation is critical for maintaining trust among member nations who must share sensitive data across a unified digital landscape.
The success of these audits has created a scalable blueprint for other government bodies looking to modernize their digital infrastructure while maintaining strict compliance. When a prestigious body like the BSI endorses a consumer platform, it removes the bureaucratic hurdles that often prevent the adoption of innovative technologies in the public sector. This exhaustive vetting process ensures that digital transformation is built on a foundation of verified, hardware-rooted security measures rather than empty promises from vendors. It also emphasizes the importance of independent oversight in the tech industry, as governmental pressure encourages manufacturers to maintain the highest possible security standards for all users. By satisfying the stringent requirements of the 32 member states, the certification proves that modern software engineering can achieve a level of resilience that was once thought impossible for mass-market products, effectively bridging the gap between civilian and military grade technology.
The Technical Infrastructure of Modern Military Security
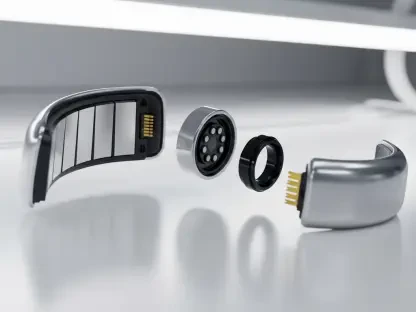
Multi-Layered Protection and Hardware Integrity
The cornerstone of NATO’s confidence in this ecosystem is the sophisticated hardware isolation provided by the Secure Enclave and the Secure Boot process. These systems act as a “computer within a computer,” managing cryptographic keys and biometric data entirely separate from the main application processor. This means that even if a device is targeted by a complex malware attack that compromises the primary operating system, the most sensitive secrets remain locked away in an inaccessible hardware vault. Furthermore, the implementation of Memory Integrity Enforcement on the latest silicon ensures that malicious code cannot manipulate the system’s memory to gain unauthorized privileges. This hardware-rooted approach provides a level of defense that software-only solutions cannot match, creating a robust environment where data remains protected from the moment the device is powered on until it is safely locked.
Building on this physical foundation, the integrated protection extends to the very DNA of the software architecture, ensuring that every layer of the user experience is monitored for irregularities. The secure boot sequence verifies the integrity of the operating system at every stage, preventing the execution of unauthorized or tampered code that could serve as a backdoor for adversaries. This continuous verification process is essential for military operations where the integrity of information is just as important as its confidentiality. By utilizing a closed ecosystem where the hardware and software are designed in tandem, Apple can enforce strict security policies that are difficult to replicate on open platforms. This holistic design philosophy ensures that there are no weak links in the chain of command, allowing NATO to maintain a consistent security posture regardless of where a device is deployed geographically.
Operational Protocols and Management Requirements
While the inherent security of the hardware is impressive, NATO’s approval is strictly contingent upon the implementation of comprehensive Mobile Device Management protocols. These MDM systems allow administrators to enforce specific usage policies, such as requiring complex passcodes and ensuring that biometric authentication like Face ID is always active. Users are restricted to utilizing native applications for sensitive tasks, which prevents the leakage of data through unverified third-party software that may not adhere to the same rigorous standards. Additionally, these managed environments allow for the remote wiping of devices in the event they are lost or captured, ensuring that classified data never falls into the wrong hands. This combination of robust hardware and strict administrative oversight creates a “managed trust” model that balances the flexibility of mobile technology with the rigid requirements of military discipline.
For personnel operating in high-threat environments, the inclusion of specialized features like Lockdown Mode provides an additional tier of defense that exceeds standard classified requirements. This mode drastically reduces the attack surface of the device by disabling certain web technologies and restricting incoming communications from unknown sources, effectively shielding the user from targeted “zero-click” exploits. Such granular control allows NATO to tailor the security level of each device based on the specific mission profile and the perceived threat level. Furthermore, the requirement to avoid unverified configuration profiles ensures that the device’s internal settings remain uncompromised by external influences. This disciplined approach to digital hygiene is mandatory for maintaining the certification, as even the most secure hardware can be undermined by poor operational practices. By combining cutting-edge technology with traditional military rigors, the alliance has created a highly resilient mobile communication network.
Broader Implications for Global Enterprise and Privacy
Closing the Gap Between Military and Consumer Grades
The fact that a standard smartphone can now meet the requirements of the world’s most powerful military alliance has profound implications for the privacy of the average citizen. It suggests that the same end-to-end encryption and hardware-based isolation used to protect a private individual’s personal photos and messages are now robust enough to safeguard national security interests. This convergence of civilian and military technology highlights a significant trend where the tech industry’s push for user privacy has inadvertently created tools that are powerful enough for international defense. It validates the idea that high-level security should not be a luxury reserved for the elite but a standard feature for everyone. This shift also challenges the notion that government-level security requires backdoors, as NATO’s reliance on these devices proves that “unbreakable” encryption is actually a strategic asset for national stability.
This closing gap also forces a re-evaluation of how we perceive “military-grade” technology, as the term now increasingly refers to products that are available at any local electronics store. As consumer platforms continue to evolve at a breakneck pace, they are often outperforming the specialized systems developed by defense departments in terms of encryption speed and threat detection. This democratization of high-end security tools empowers individuals and small organizations to protect their data against the same types of sophisticated adversaries that target nation-states. It also fosters a more competitive environment for tech manufacturers, who must now vie for government contracts by proving that their consumer products are inherently secure. Ultimately, this trend leads to a more secure digital world for everyone, as the innovations driven by the needs of an alliance like NATO eventually trickle down to improve the safety of the entire global internet ecosystem.
Strengthening Corporate Confidence in Mobile Platforms
For the global enterprise sector, NATO’s endorsement acts as a powerful signal of reliability that simplifies the complex process of hardware procurement. Large-scale organizations often struggle with the “bring your own device” dilemma, but the certification of standard iOS hardware provides a clear path forward for IT departments. If a device is deemed secure enough for NATO-restricted information, it is logically more than sufficient for the proprietary data and trade secrets of a multinational corporation. This allows businesses to deploy standard hardware across their workforce without the need for expensive, specialized modifications or additional security software that can degrade performance. The result is a more streamlined operational model where employees can use the tools they are already familiar with, while the organization benefits from a battle-tested security architecture that mitigates professional-grade risks.
In the future, organizations should look beyond traditional security perimeters and focus on adopting platforms that offer hardware-rooted integrity as a native feature. Decision-makers ought to prioritize devices that have undergone third-party governmental auditing, as these evaluations provide a level of assurance that internal testing cannot match. Moving forward, the focus must shift toward comprehensive Mobile Device Management to ensure that even the most secure hardware is used within a disciplined framework. This approach not only protects sensitive assets but also enhances employee productivity by providing them with reliable, high-performance tools. By aligning corporate security strategies with the standards set by international defense organizations, businesses can ensure they are prepared for the evolving threat landscape of the late 2020s. This proactive stance on mobile security will be the defining factor for success in an era where data is the most valuable commodity.
The transition toward consumer-grade hardware within NATO was a calculated move that prioritized long-term resilience over legacy protocols. By leveraging the security innovations of the private sector, the alliance successfully modernized its communication infrastructure without compromising on its rigorous safety standards. This shift proved that integrated, hardware-rooted protections are far superior to the fragmented security models of the past. As a result, the alliance was able to deploy advanced mobile capabilities across all member states, ensuring that personnel remained connected through a secure and efficient network. This milestone set a new benchmark for the tech industry, demonstrating that mass-market electronics can indeed meet the demands of global defense operations.