The digital landscape has recently been unsettled by the emergence of a highly sophisticated exploit chain known as DarkSword, which represents a fundamental shift in how mobile devices are compromised today because it bypasses the traditional user-reliance on clicking suspicious links or downloading dubious attachments. Unlike the malware of previous years that required a specific human error, this particular threat utilizes a sequence of vulnerabilities to execute a silent intrusion through standard web browsing activities. The sheer complexity of this tool allows it to circumvent the once-impermeable layers of the iOS sandbox, granting unauthorized access to a vast array of sensitive information including private text messages, high-resolution photographs, and real-time location tracking data. This vulnerability has turned the simple act of visiting a compromised, yet otherwise legitimate, news or shopping website into a potential gateway for total device takeover. The realization that such an advanced tool can be deployed without a single interaction from the owner has sparked widespread concern among cybersecurity experts and the general public alike.
The Mechanics of Modern Exploitation: A New Frontier
The specific methodology utilized by DarkSword involves a multi-stage execution process that targets the rendering engine used by mobile browsers to display content. By injecting malicious code into the back-end of popular websites, attackers can trigger a silent download and execution of the payload as soon as the page finishes loading in the browser. This method effectively neutralizes the effectiveness of traditional security training, which often emphasizes the avoidance of untrustworthy domains or unverified email senders. Once the initial breach occurs, the exploit chain moves laterally through the operating system, escalating privileges until it reaches the kernel level where it can exert complete control over the hardware functions. This capability includes the activation of the microphone and camera, the exfiltration of encrypted keychain data, and the installation of persistent spyware that remains on the device even after a restart. The sophistication of this approach highlights a growing trend where attackers prioritize stealth and reliability over high-volume distribution.
Compounding the danger of this specific exploit is its widespread availability on public coding repositories like GitHub, which essentially democratizes state-level hacking capabilities for a global audience of malicious actors. This transition from a private, state-sponsored tool to an open-source kit means that even individuals with moderate technical skills can now launch attacks that were previously the exclusive domain of elite intelligence agencies. Security researchers at firms like Jamf have noted that this availability has led to a rapid diversification of the ways DarkSword is being integrated into broader cybercrime operations. The tool is no longer just a scalpel for targeted espionage but has become a Swiss Army knife for data theft, financial fraud, and digital stalking. This accessibility necessitates a paradigm shift in how individual users perceive their personal digital security, moving away from the assumption that they are too insignificant to be targeted. When a tool is this readily accessible, the cost of deployment drops significantly, making the average smartphone user a viable target.
Apple’s Multi-Tiered Response: Bridging the Security Gap
Recognizing the unprecedented threat posed by this exploit chain, Apple has initiated a comprehensive software deployment strategy that spans nearly a decade of hardware iterations. The primary fix is bundled within the latest iOS 26.4 release, which provides the most robust defenses and structural changes to the browser architecture to prevent memory corruption. However, the company has also acknowledged that a significant portion of its user base remains on older versions for various reasons, ranging from hardware limitations to personal preference regarding interface design. To address this, security engineers backported critical patches to older operating systems, releasing iOS 18.7.7 for those who have intentionally avoided the newer software ecosystem. Even more remarkably, updates were issued for legacy versions like iOS 15 and 16, ensuring that devices as old as the 2015 iPhone 6s are protected against the DarkSword toolkit. This extensive support cycle demonstrates a corporate commitment to security that transcends the typical planned obsolescence cycles.
The decision to provide updates for older operating systems also addresses a specific tension within the community regarding the “Liquid Glass” design language introduced in the most recent major OS updates. Many users have expressed a preference for the more tactile and traditional aesthetic of previous iterations, leading them to delay or entirely refuse upgrades that would alter the visual experience of their devices. By decoupling these aesthetic changes from vital security patches, the manufacturer has ensured that safety is not a luxury reserved only for those who embrace the latest design trends. This approach acknowledges that the user experience is subjective, while the requirement for data integrity is absolute and non-negotiable in the modern era. However, this fragmented update landscape also places a greater burden of responsibility on the user to verify which version is appropriate for their specific hardware and software configuration. The availability of these patches is only effective if they are proactively installed, highlighting the critical role of user agency.
The Path to Resilience: Implementation and Action
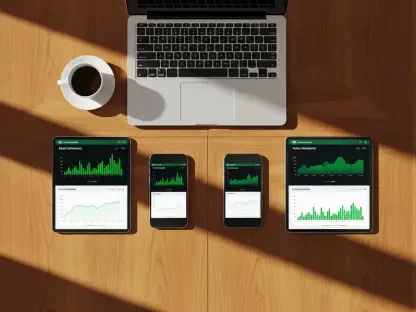
Current data from industry monitoring groups suggests that approximately twenty percent of active iPhones are currently operating with outdated software, leaving a massive global population vulnerable to the DarkSword exploit. This statistical reality underscores the difficulty of achieving universal security coverage, even when the necessary tools and patches are readily available to the public. For individuals seeking to verify their status, the process involves navigating through the general settings of the device to check for available software updates. It is vital to recognize that the protection offered by these patches is not retroactive; any compromise that occurred prior to the update may still persist in the form of dormant spyware or compromised credentials. Therefore, the update should be viewed as a foundational step in a larger security hygiene routine that includes periodic password changes and the use of multi-factor authentication. The urgency of this action cannot be overstated, as the window of opportunity for attackers remains open as long as the device continues to run on vulnerable code.
The resolution of the crisis was achieved through a combination of rapid engineering and a shift toward more inclusive security maintenance practices that respected the diversity of the user base. It was determined that the most effective path forward involved a total audit of web-rendering vulnerabilities and the implementation of more aggressive memory protection protocols across all supported devices. Users were encouraged to transition toward a zero-trust model of mobile browsing, where the integrity of every website was verified through real-time security cloud checks. Moving forward, the industry learned that the democratization of hacking tools required an equally democratic approach to security, where protection was not dictated by the age of the hardware. The successful deployment of these patches served as a vital blueprint for addressing future zero-day exploits that might emerge from open-source communities. By prioritizing the sealing of the DarkSword entry points, the security community established a higher standard for digital resilience that transformed mobile privacy.