The rapid migration of critical financial and healthcare infrastructure to mobile platforms has fundamentally altered the global threat landscape by moving the primary attack surface from centralized servers to millions of unmanaged user devices. While traditional security models were designed for a web-centric era where organizations maintained a clear perimeter around their data, the current reality involves deploying sophisticated application binaries directly into potentially hostile environments. Recent industry data reveals that 43% of organizational security breaches now originate at the mobile edge, underscoring a dangerous gap between existing DevSecOps practices and the unique requirements of mobile architecture. Many teams continue to rely on legacy Static Application Security Testing tools that were originally built to scan server-side code, failing to recognize that a mobile app functions more like a messenger operating in enemy territory rather than a protected gateway. This architectural divergence necessitates a total reassessment of trust assumptions, moving away from the “fortress” mentality of the past toward a model that assumes the client device is already compromised or under active observation by a malicious actor.
Defending Against Man-at-the-End Attacks
The most significant challenge facing contemporary mobile security teams is the rise of man-at-the-end attacks, a scenario where the adversary has complete physical and administrative control over the device hosting the application. Unlike traditional web environments where the server binary remains hidden behind layers of firewalls and virtual perimeters, a mobile application binary is physically present on the user’s hardware, making it a target for deep inspection and reverse engineering. Attackers utilize sophisticated dynamic instrumentation toolkits, such as Frida, to inject custom code into a running process’s memory space, effectively bypassing logical checks that would remain secure in a standard web environment. This capability allows for inline hooking and the interception of the Procedure Linkage Table or Global Offset Table, enabling an attacker to redirect execution flows toward malicious functions. Consequently, logic that appears sound during static analysis can be completely subverted at runtime, turning a secure authentication routine into a “fail-open” gateway that grants unauthorized access without ever interacting with the backend security protocols.
To address these vulnerabilities, modern DevSecOps pipelines must integrate Runtime Application Self-Protection mechanisms that actively monitor the application’s integrity from within the process itself. Rather than relying solely on obfuscation techniques like control flow flattening or symbol stripping, which only delay an experienced attacker, RASP systems provide a dynamic defense by scanning for specific artifacts indicative of compromise. This includes monitoring for named pipes used by hooking frameworks or inspecting memory maps for unauthorized library injections that deviate from the signed application package. Furthermore, organizations are increasingly adopting hardware-backed attestation services, such as the Android Play Integrity API, to receive cryptographically signed tokens from the operating system that confirm the device environment remains secure. By requiring these tokens before granting access to sensitive APIs, developers can ensure that the application is not running in a rooted environment or within an emulator designed for large-scale data scraping, effectively restoring a layer of trust in the client-side execution environment.
Hardening DatThe Role of Hardware-Backed Cryptography
A recurring architectural failure in mobile development involves the reliance on software-based encryption methods that provide a false sense of security while leaving master keys vulnerable to extraction. Many development teams implement standard encryption libraries for local storage but commit the critical error of storing the resulting keys within the application’s private directory or in a obfuscated string within the code. In a rooted or compromised environment, the operating system’s sandbox is effectively transparent, allowing attackers to utilize memory dumps or backup exploits to scrape these keys and decrypt local databases containing sensitive user information. This approach is the digital equivalent of hiding a spare house key under a doormat; it may deter a casual observer, but it offers zero resistance to a motivated intruder who understands the underlying structure of the system. Without a hardware-bound root of trust, software encryption remains a fragile layer of defense that can be stripped away as soon as the application process is attached to a debugger.
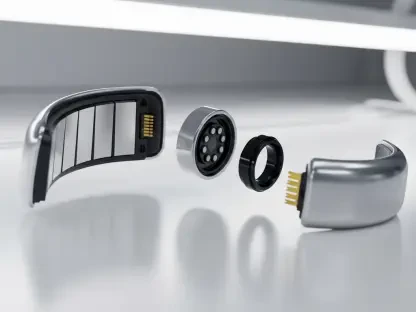
To eliminate this vulnerability, security architects must enforce a strict policy of cryptographic binding to the hardware layer of the mobile device. This is achieved by utilizing the Trusted Execution Environment or the Secure Enclave to handle all sensitive cryptographic operations, ensuring that private keys never enter the application’s main memory space where they could be intercepted. In this model, the application sends raw data to the hardware component, which performs the encryption or decryption internally and returns only the processed result, keeping the keys themselves physically isolated from the primary processor. High-security applications, particularly in the fintech and healthcare sectors, are also incorporating user-presence requirements that link cryptographic access to biometric prompts. By requiring a successful Face ID or fingerprint scan to unlock a specific key, developers create a cryptographic “proof of presence” that protects data even if the device is stolen while in an unlocked state. This strategy transforms the mobile device from a potential liability into a robust security token that leverages hardware isolation to protect the most sensitive organizational assets.
Mitigating Logic Entropy in AI-Assisted Development
The rapid adoption of AI-assisted development tools has significantly increased the velocity of mobile app releases, but it has also introduced a phenomenon known as logic entropy into the DevSecOps pipeline. As developers rely more heavily on AI to generate boilerplate code and complex functions, there is a growing trend of “insecure by default” patterns entering production environments because the underlying models are often trained on legacy repositories containing outdated security protocols. Research indicates that AI-assisted developers are nearly 80% more likely to introduce vulnerabilities like plaintext credentials, weak random number generators, or deprecated Transport Layer Security versions into their code. This occurs because the AI prioritizes functional correctness and statistical commonality over security best practices, leading to a situation where a developer might unintentionally skip certificate pinning or use an insecure trust manager simply because the AI-suggested snippet worked immediately during the testing phase.
To counter the risks associated with AI-generated code, organizations must treat these tools as untrusted contributors and implement specialized automated checks within the continuous integration and delivery pipeline. This requires the creation of custom linting rules and static analysis policies that specifically target the common shortcuts taken by AI models, such as the use of the “AllowAllHostnameVerifier” or other fail-open configurations. DevSecOps teams are also focusing on the enforcement of a comprehensive Software Bill of Materials to validate every dependency suggested by an AI assistant against global vulnerability databases before it is integrated into the build. By maintaining a rigorous human-in-the-loop review process for AI-generated logic and using automated tools to verify the security parameters of every function, teams can harness the speed of AI while preventing the gradual erosion of the application’s security posture. This proactive stance ensures that the increased development speed does not result in a corresponding increase in the technical debt associated with unaddressed security vulnerabilities.
Strategic Responses: iOS Sideloading and Integrity Risk
Recent regulatory shifts in the mobile ecosystem, specifically the introduction of alternative app marketplaces and sideloading on platforms like iOS, have created a new vector for repackaging attacks that organizations can no longer ignore. While these changes were intended to foster competition and give users more choice, they have also simplified the process for malicious actors to distribute modified versions of popular applications. In a repackaging attack, an adversary takes a legitimate application binary, injects a malicious library or tracking script using dynamic instrumentation techniques, and then re-signs the application with a stolen or leaked enterprise certificate. Because the certificate appears valid to the operating system, the user is often presented with fewer warnings than they would see with an unsigned app, leading them to believe they are using a safe, albeit unofficial, version of the software. This creates a significant risk for enterprises whose brand reputation and user data are tied to the integrity of their mobile presence, as these “cracked” versions can act as persistent surveillanceware.
To maintain security in this fragmented distribution environment, applications must incorporate self-verification routines that check their own signing identity at runtime to ensure they are running in the intended state. This process involves comparing the fingerprint of the active signing certificate against a hardcoded hash of the official production key, a technique that allows the app to detect if it has been re-signed by an unauthorized third party. Security teams recognized that relying on the operating system’s built-in checks was no longer sufficient, leading to the implementation of automated responses that trigger when a mismatch is detected. When an app identified that its integrity had been compromised, it immediately terminated the active session, cleared all data from the hardware-backed keystore, and sent an alert to the backend server to blacklist the device. These actions transformed the application into a self-protecting entity that could survive in a hostile environment, ensuring that the value of any stolen data was minimized by the difficulty of the extraction process. Moving forward, organizations must continue to prioritize these resilient architectures as the boundaries between official and unofficial software distribution channels continue to blur.