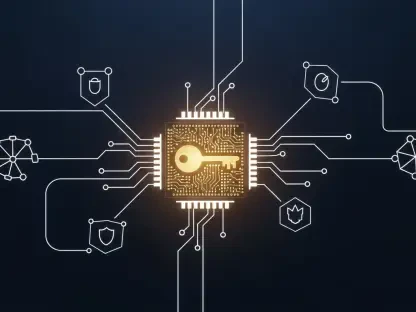
With the cyber threats faced by mobile phone users uprising at an alarming rate, app permissions became a crucial step in securing our devices. Kaspersky Lab detected almost 6 million malicious installation packages and more than 94.000 mobile banking Trojans.
Mobile apps need permissions in order to work, but in the eye of the regular smartphone user, today’s breed of mobile software seems to make unreasonable demands before allowing you to install them. We must pay extra attention because these requests may be hiding unscrupulous or even malicious intentions. Read below a step-by-step guide to app permissions and how you can take full control of your shared data.
What are app permissions and why the requests should make sense to users
In order to perform its full range of functions, an app needs some concessions or allowances that users agree with. In theory, an app developer must be transparent in how the data is handled, including information provided by a user, collected about a user, and collected about a user’s use of the app or device. However, cybercriminals can exploit them for their personal gain. For the regular user, the permissions protocol can be extremely confusing, especially if so many are presented at once, with little clarification about what they’re actually used for and even less understanding of the potential consequences.
Normal and dangerous permissions
System permissions are divided into two groups: normal and dangerous. Because they don’t pose a risk to our privacy, normal permissions are allowed by default. For example, Android allows apps to access the internet without asking for your permission. On the other hand, Android will always ask the user to approve dangerous permissions, such as calling history, private messages, location, microphone, SD card. Recently, Trustlook has identified 25,936 malicious apps that are currently using one of Facebook’s APIs, such as a login API or messaging API. These allow apps to access a range of information from Facebook profiles, like name, location, and email address. “To be fair, Facebook is not the only company with its APIs embedded in malicious applications. Twitter, LinkedIn, Google, and Yahoo offer similar options to developers, and thus their user data faces similar exposure”, according to the same article.
Top potentially dangerous permissions
You should keep an eye out for apps that request access to the following permission groups, as approving a single permission from any group automatically approves all other permissions within that same group. The ups and downs for each permission:
Phone details
This type of permissions allows apps to know your phone number, current mobile network information, and ongoing call status. Granting access to your phone details means that an app can read and send the IMEI of your phone via the Internet. Apps can also make calls, see who’s calling you, read and edit your call logs, add voicemail, and even redirect calls to other numbers.
Fair use: Communication apps need this permission to function properly. Some apps offer customer support via telephone, thus allowing you to call a number directly from the app.Dangers: By storing your phone’s IMEI on their servers, cybercriminals can track your device without using more personal information. Furthermore, a malicious app can make calls without your consent, including paid calls.
Location
These types of permissions allow apps to read and use the device’s approximate or precise location, using cellular base stations, Wi-Fi hotspots or GPS.
Fair use: navigation apps, camera apps (geo-tag your photos), shopping apps, check-in features in apps like Facebook.Dangers: Cybercriminals can use location data to track the device and gather data on its user. Gathered data can then be correlated with other pieces of information so they can send phishing emails or messages. By tracking your phone, thieves know when you’re not at home.
Storage
Storage permissions allow apps to access and modify the files stored on your device, like music, photos, documents or something else.
Fair use: music apps, camera apps, social networking apps, document apps, browsers.
Dangers: Without your knowledge, a malicious app can read, change, and delete documents, photos and any other files. From there, a malware infection can spread rapidly.
SMS and MMS permissions
This permission grants apps access to read and send text messages, as well as receive WAP push messages and MMS messages.
Fair use: Communication and social media apps need this permission to function properly.
Dangers: A malicious app can use your phone to spam others and even subscribe to paid services without your knowledge. By reading two-step verification codes, hackers can easily access your bank account by correlating the code with the internet banking login information.
Contacts
Apps usually request access to your contacts so you can share things. This permission allows apps to read, create, or edit the contact list, as well as access the list of all accounts used on the device, including Facebook, Instagram, Twitter, Google etc.
Fair use: Many apps need this permission to function properly, like communication apps or social media apps.
Dangers: With the entire contact list at its disposal, a malicious app can target your friends, family, and co-workers with spam messages or phishing scams.
The first step in order to keep your device clean is to install apps from an approved app store. Before installing an app, take some time to read its boring description which includes permissions list, Terms, and Conditions or even user reviews. Always remember that app permissions exist to protect the end user and if you go through the permission list using logic and common sense you should be able to take full control of the data you share.