The fundamental insecurity of modern telecommunications has long been an accepted trade-off for global connectivity, yet a significant shift in capital is now challenging that status quo. Cape, a pioneering mobile carrier based in the United States, recently secured $100 million in Series C funding to accelerate the deployment of its privacy-centric cellular infrastructure. Led by prominent investors including Bain Capital Ventures and IVP, this latest financial injection elevated the company’s total capital to approximately $191 million and pushed its market valuation toward the $900 million mark. The primary objective behind this massive investment is to dismantle the traditional telecommunications landscape, which has historically relied on invasive data-tracking practices and inherently insecure signaling protocols. By targeting the vulnerabilities found in legacy systems, this initiative aims to protect users from the constant logging of location history, application activity, and sensitive communication records that often lead to catastrophic data breaches.
Engineering a Secure Communications Core
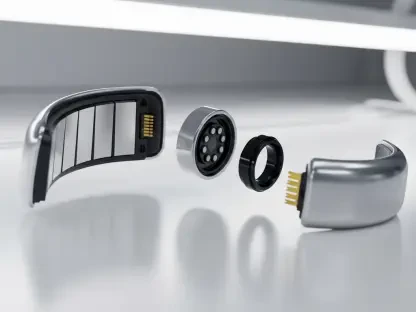
A central pillar of this technological evolution is the integration of advanced privacy tools directly into the hardware and network architecture, moving far beyond the superficial software layers used by traditional providers. One of the most significant innovations introduced is a feature known as Identifier Rotation, which periodically refreshes a device’s digital signature to prevent long-term surveillance and persistent tracking by third parties. This capability is made possible because the company is building its own mobile core network and proprietary SIM technology from the ground up, rather than simply reselling existing services. Users are granted the ability to attach multiple phone numbers to a single physical SIM card while benefiting from end-to-end encrypted communications that remain shielded from the carrier itself. By establishing a sovereign network core, the system effectively eliminates the metadata trails that hackers and state actors typically exploit to monitor high-value targets.
This radical shift in network design serves as a direct response to a decade of escalating data leaks and multi-million dollar regulatory fines levied against major telecommunications conglomerates. Conventional carriers have consistently struggled to secure private caller information, often failing to implement modern cryptographic standards within their aging infrastructures. The reliance on legacy systems meant that metadata—the digital breadcrumbs of who a person calls and where they are—was essentially public property for anyone with the right access. In contrast, the development of a privacy-first core ensures that such information is never generated or stored in a way that can be linked back to an individual user’s permanent identity. This proactive approach to security addresses the root cause of digital vulnerability rather than merely reacting to threats as they emerge. Consequently, the architecture transforms the mobile phone from a potential tracking device into a secure communication endpoint suitable for the modern era’s heightened threat environment.
Strategic Implementation and Commercial Expansion
To achieve rapid scale without sacrificing the integrity of its security protocols, the company operates as a specialized mobile virtual network operator that maintains absolute control over its own secure core infrastructure. While it utilizes the physical cell towers of established giants for broad coverage, every packet of data is routed through a private, audited environment that enforces strict anonymity. This hybrid operational model allows for a swift nationwide rollout while ensuring that no third-party entity can inspect or intercept user traffic. The initial adoption of this technology was driven by defense organizations and national security professionals who required untraceable mobile connectivity for sensitive operations. Following successful pilot programs with these government agencies, the service transitioned to a broader market in 2025, reaching corporate executives and privacy-conscious consumers who are increasingly wary of commercial surveillance. This expansion demonstrates a growing consensus that standard mobile networks are no longer sufficient for protecting personal or corporate data.
The successful funding round signaled a turning point for the industry as it moved toward a model where privacy was a default setting rather than a premium add-on. Stakeholders recognized that the next logical step involved a comprehensive audit of corporate mobile fleets to identify where metadata leakage posed the greatest risk to intellectual property. Security experts recommended that organizations began prioritizing carriers that provided hardware-level anonymity through identifier rotation and encrypted core routing. Furthermore, the transition to these secure networks necessitated a reevaluation of how mobile devices handled sensitive authentication tokens and location-based services. Individuals who sought to regain control over their digital footprints found that switching to specialized providers offered the most effective defense against persistent surveillance. As the technology matured, it became clear that integrating privacy-first protocols into the standard telecommunications stack was the only viable path forward for maintaining digital sovereignty.